Trending about Operating Systems

news
'Tis the Season to Be Naughty: 10 Awfully Inexcusable Office Pranks

forum
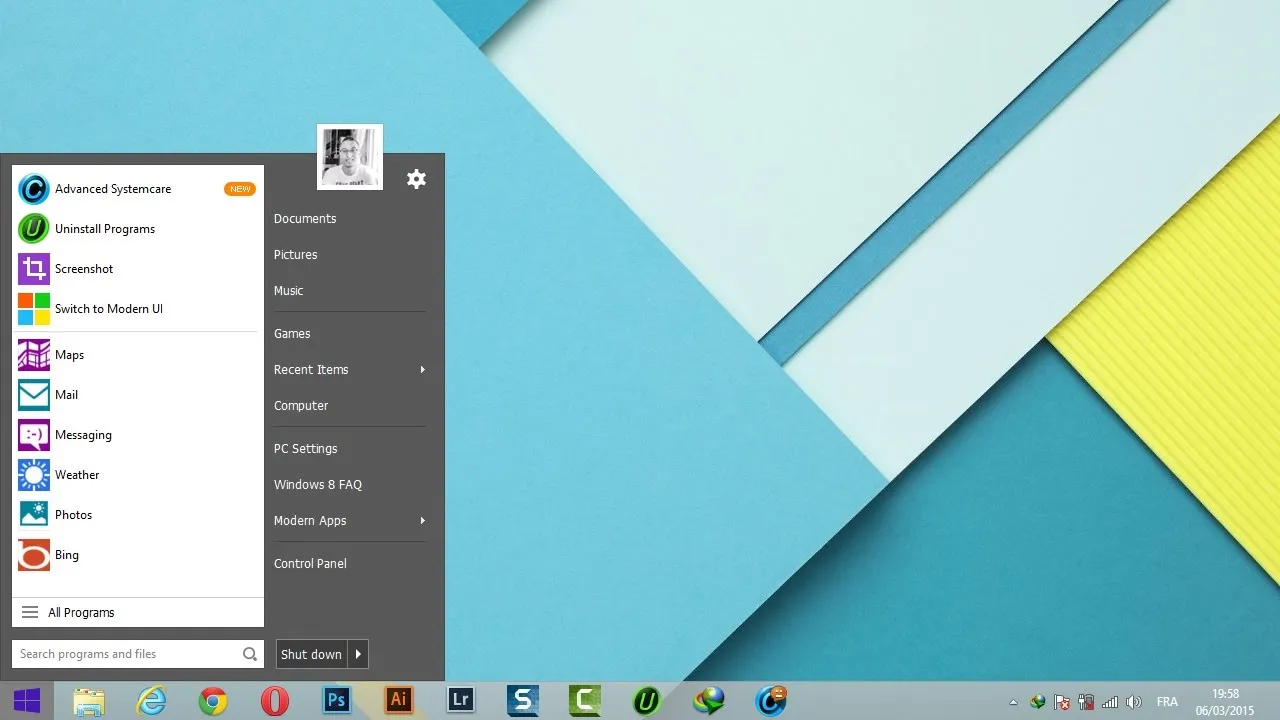
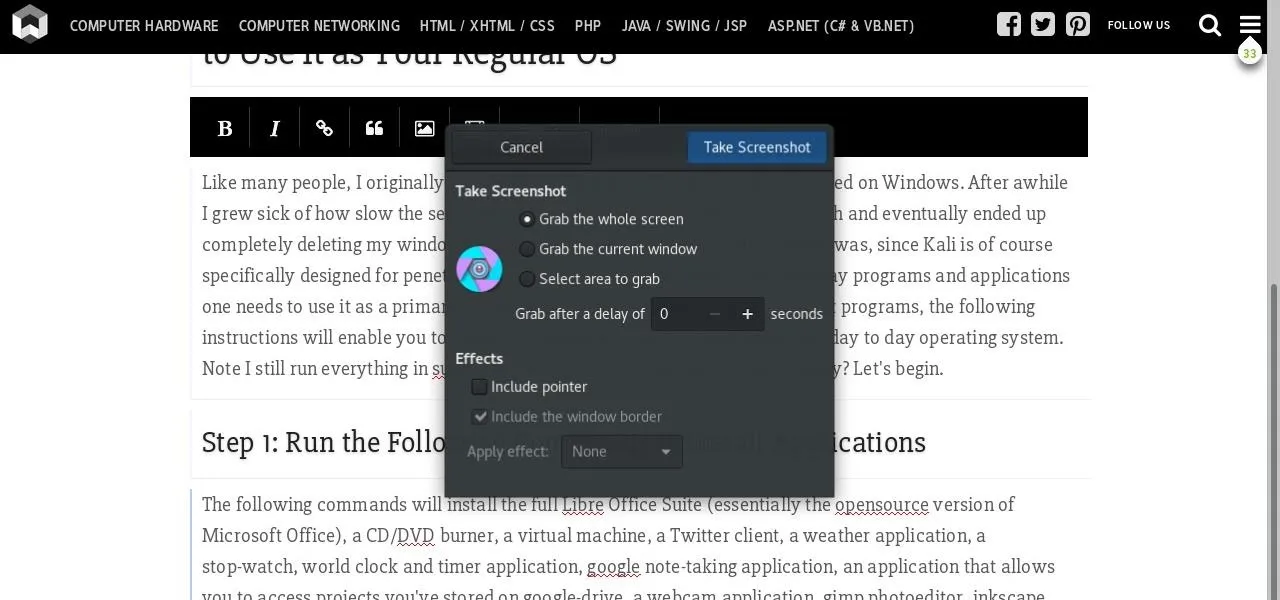
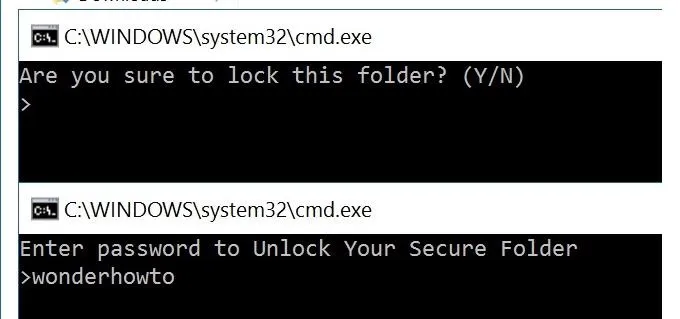
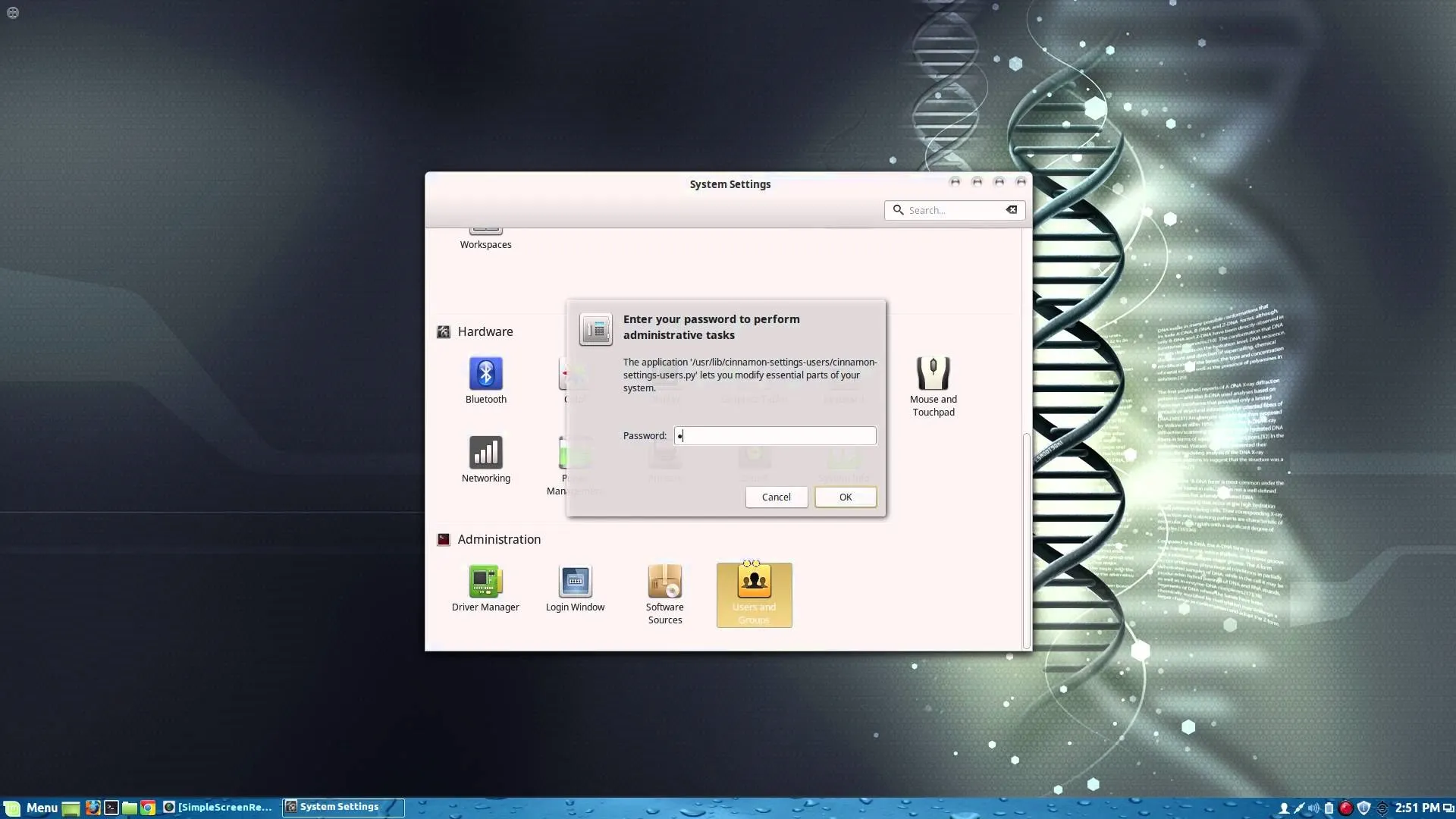
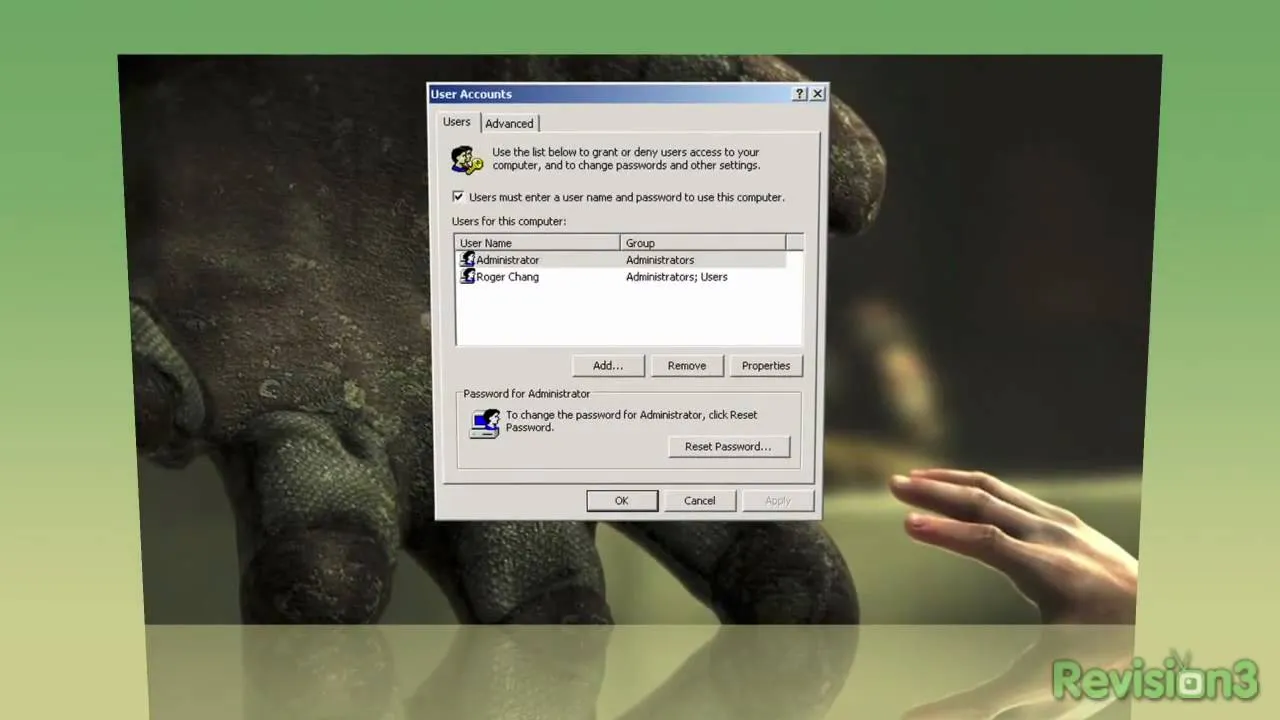
How to Speed Up Windows User Login Speed

forum
How to Disable Automatic Windows Updates





















Featured On WonderHowTo:
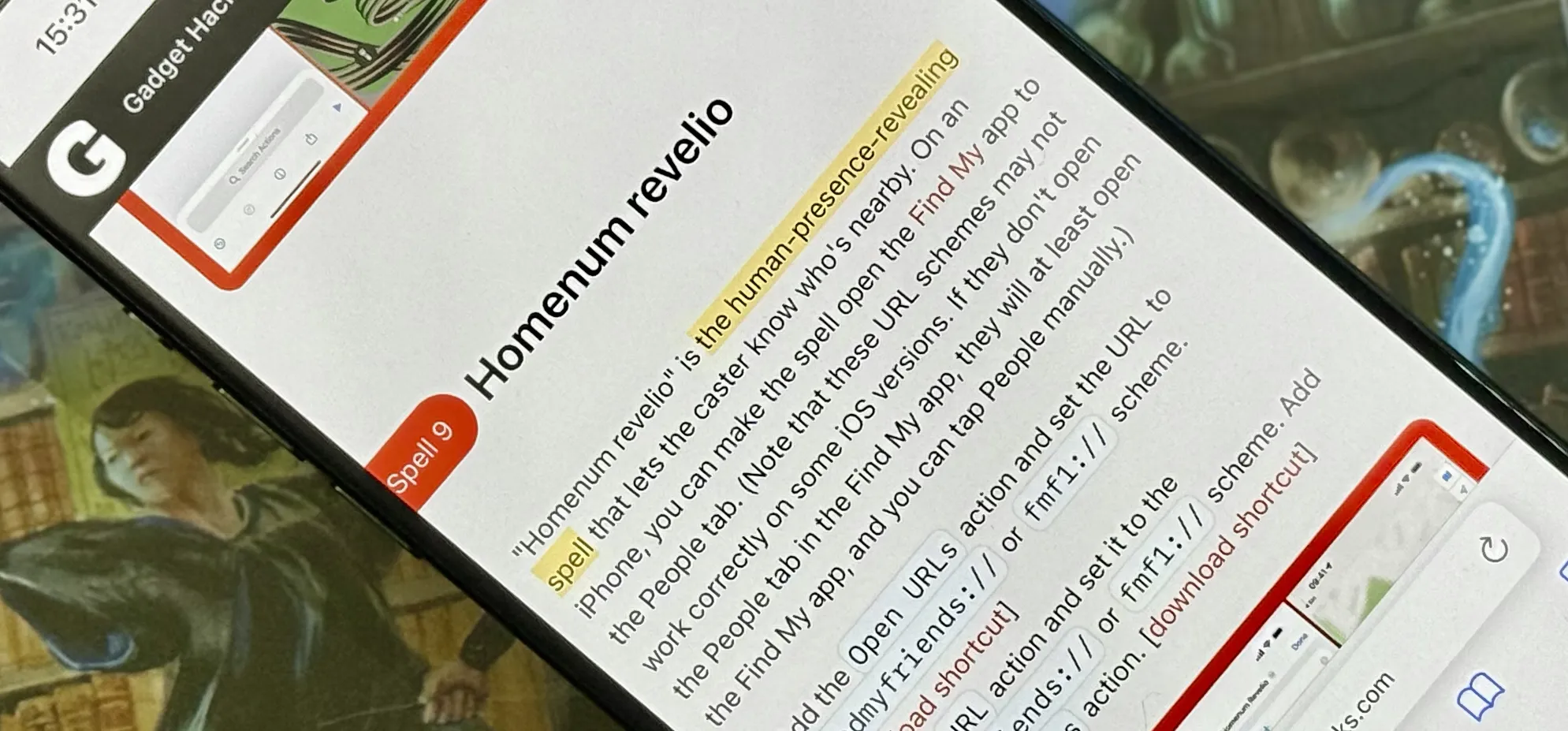
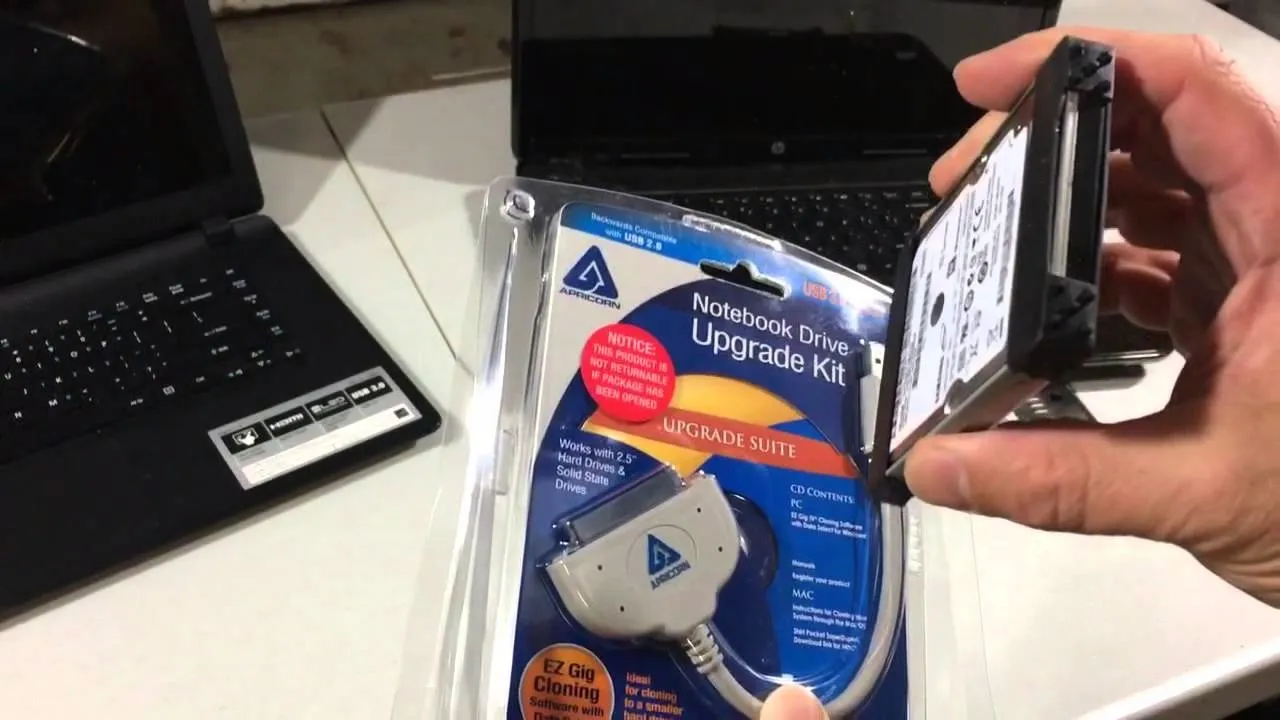
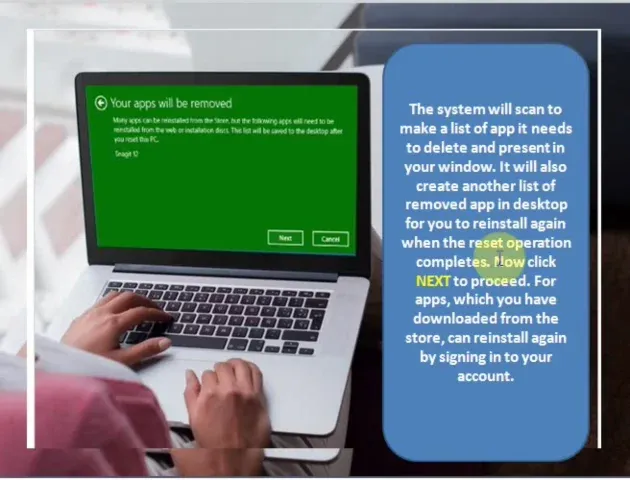
Productivity & Shortcuts










Featured On WonderHowTo:
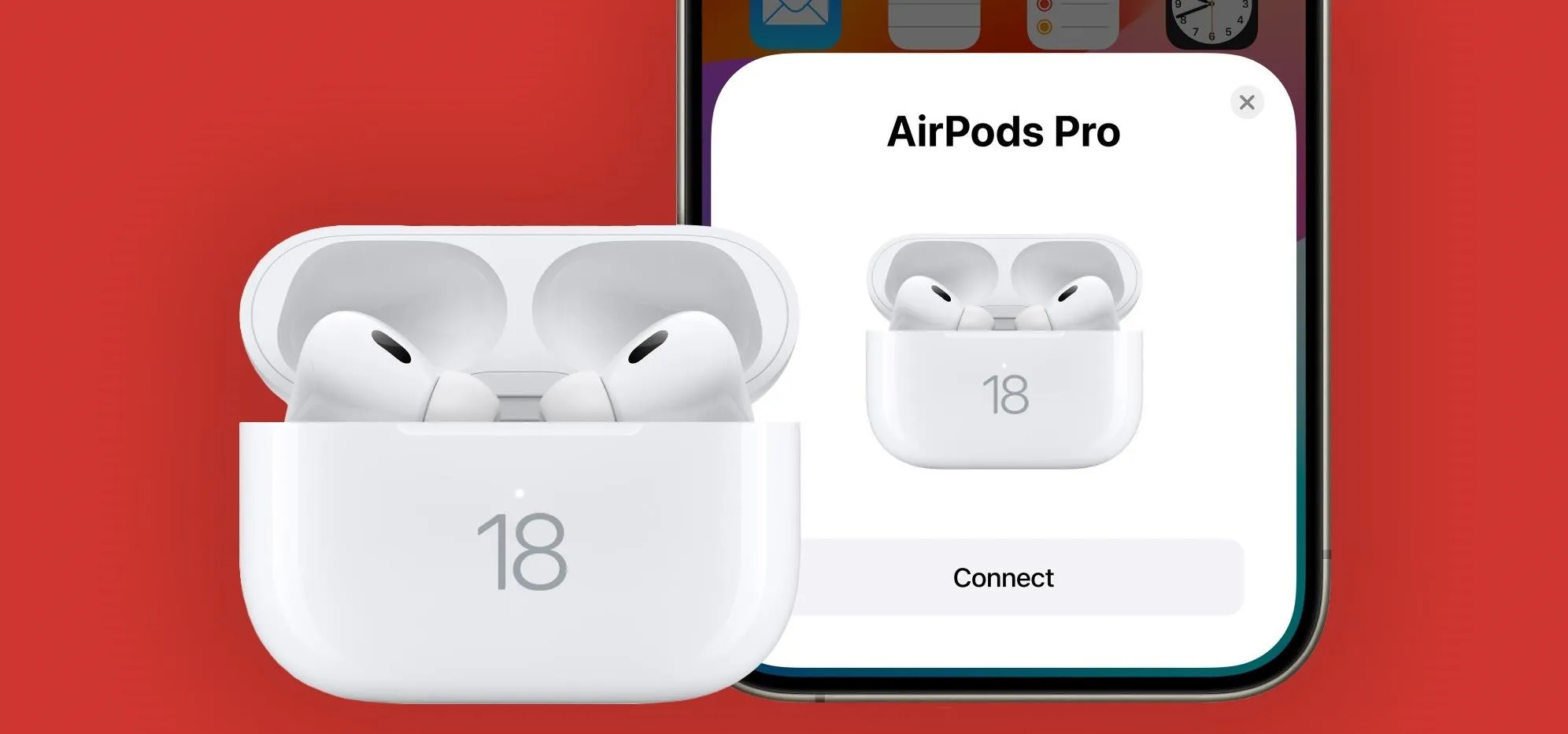
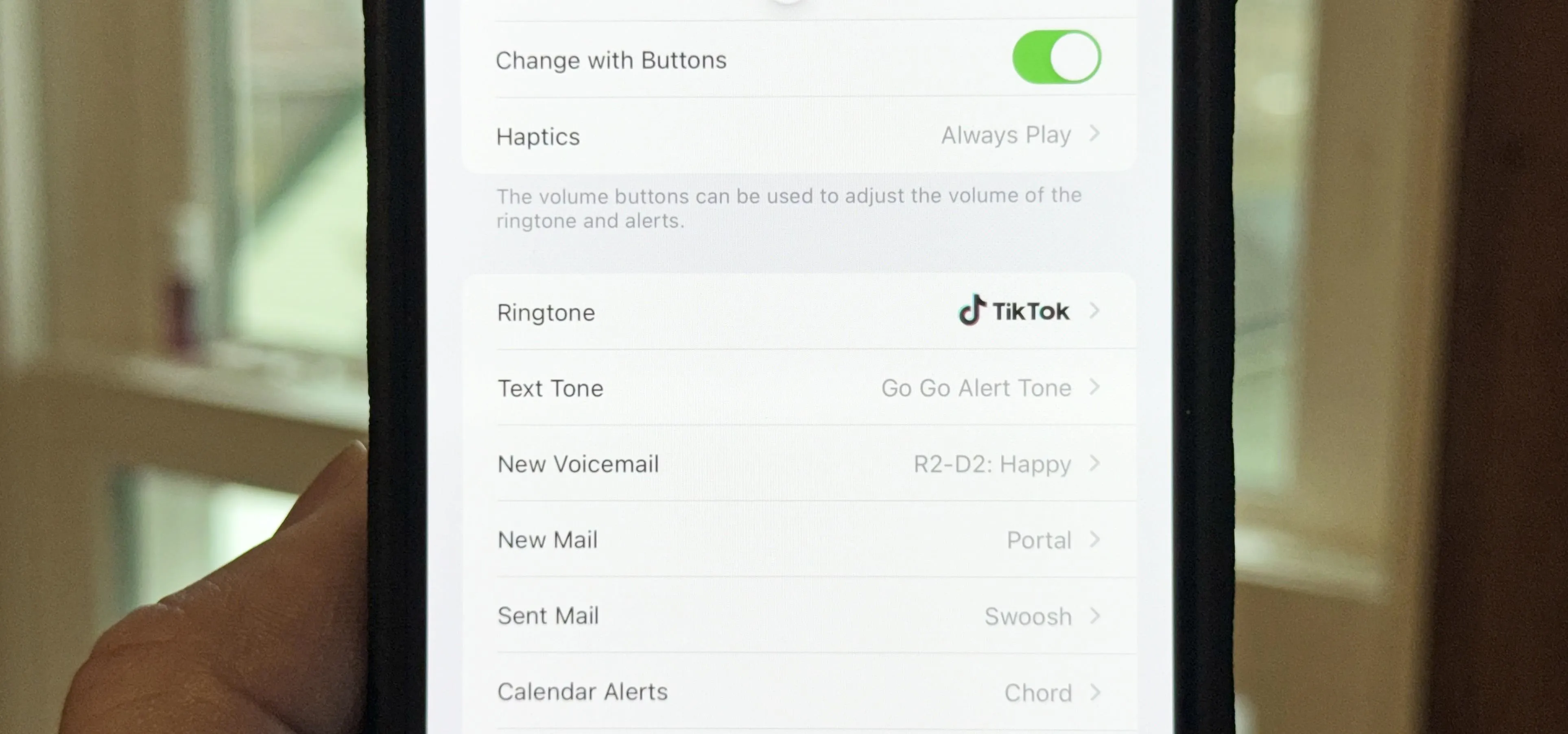
Music & Audio







Featured On WonderHowTo:
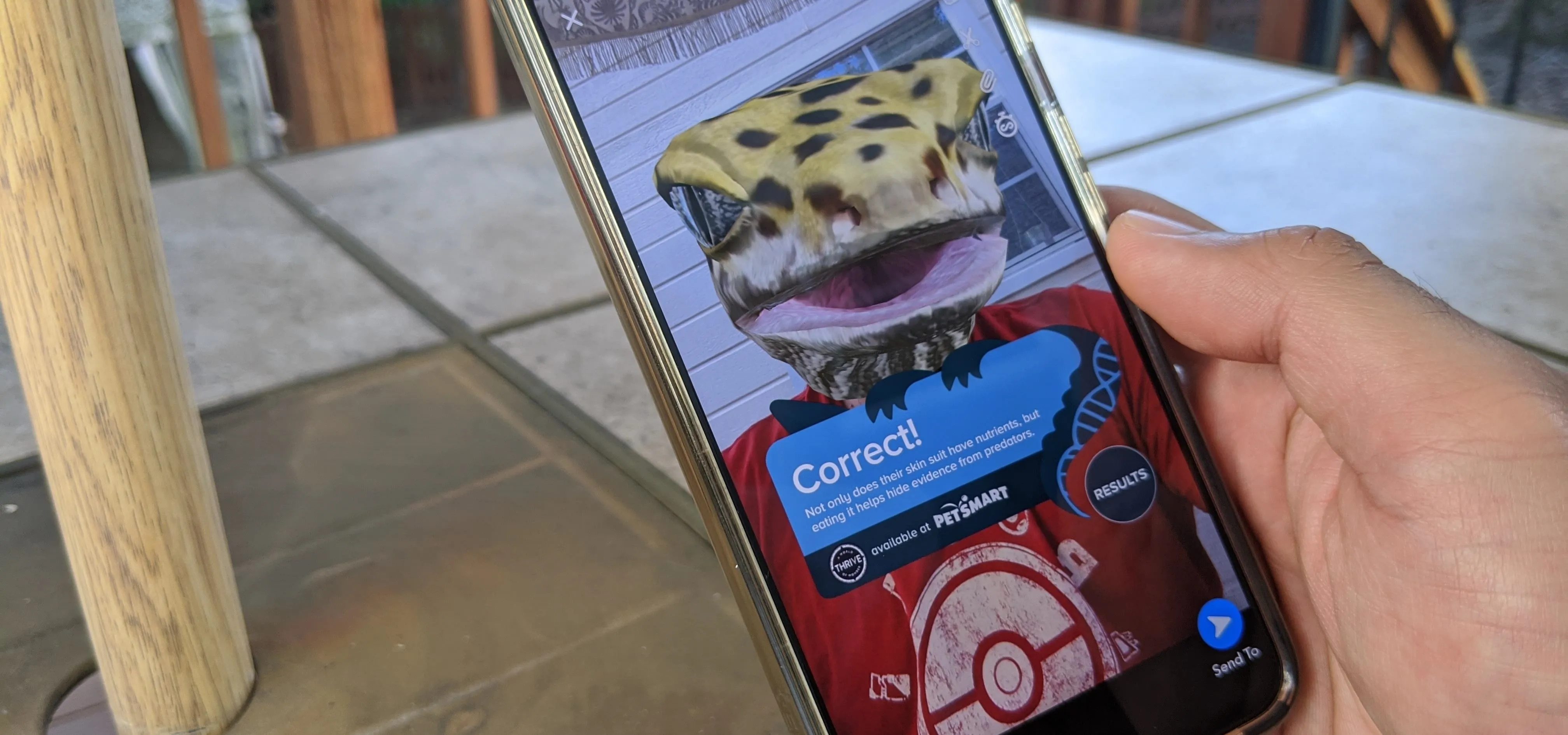
Augmented Reality






Featured On WonderHowTo:
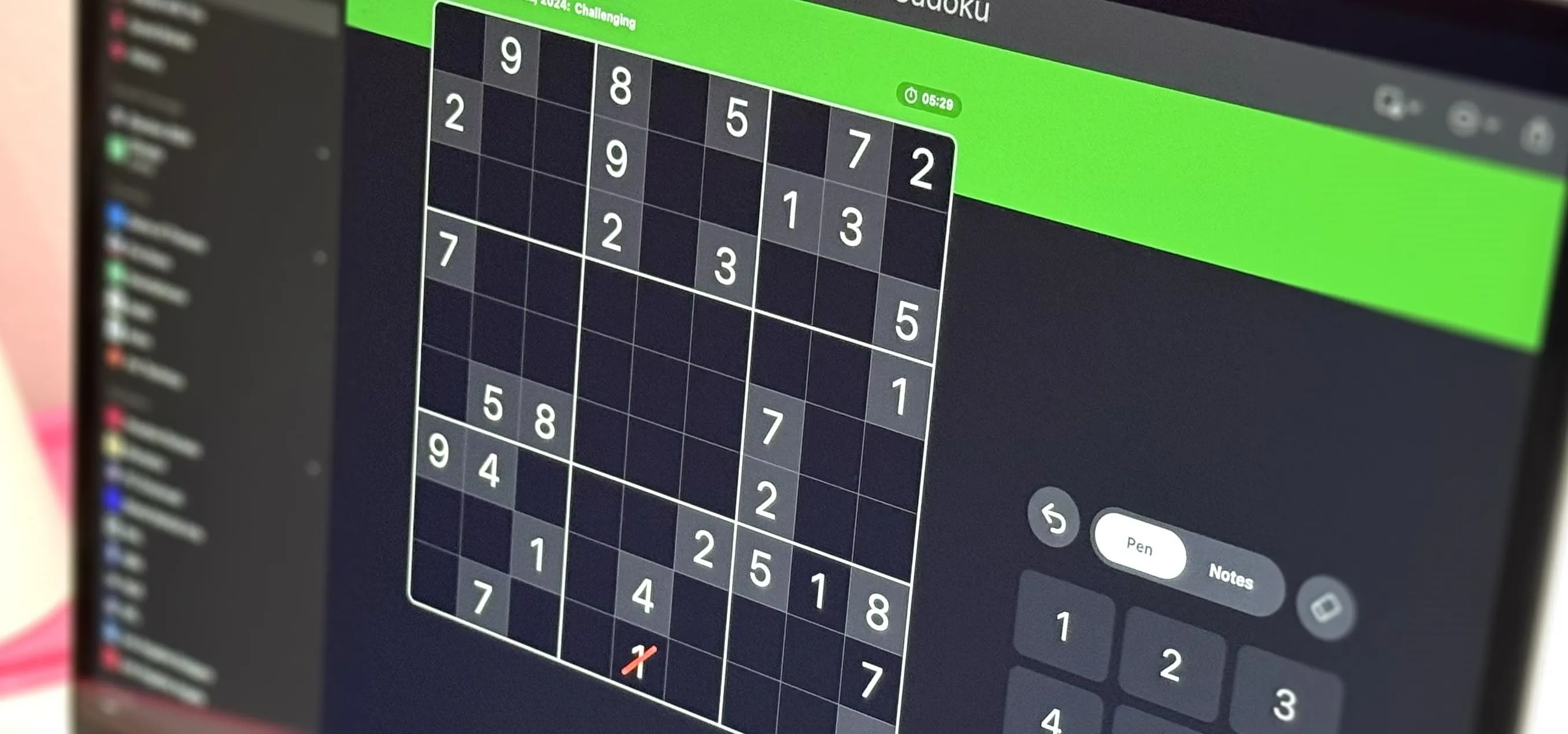
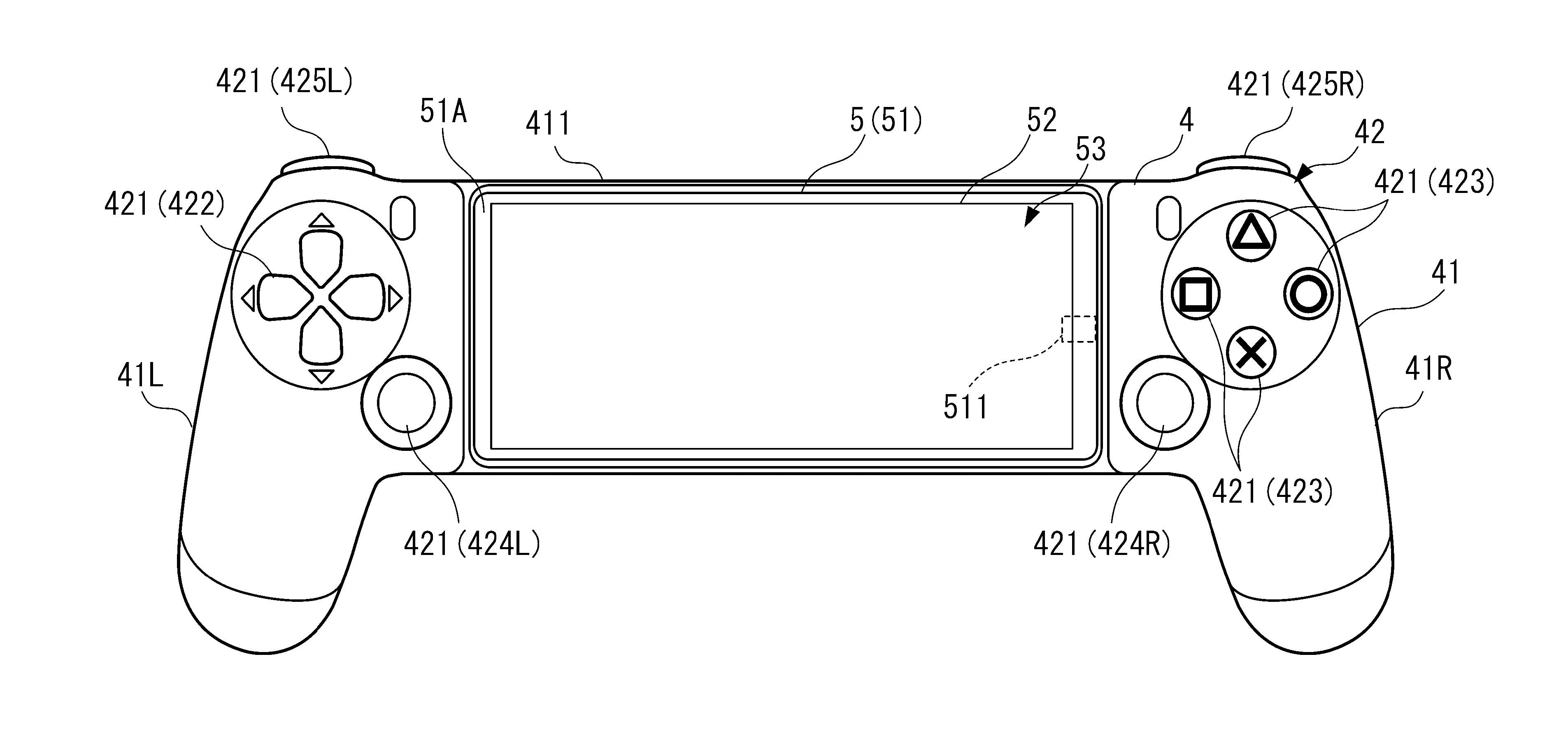
Gaming